Multi-Factor Authentication (MFA) is commonly used to protect your information online. However, MFA is not impenetrable from Social Engineering
If a password is compromised, hackers can deploy several tactics to get around any MFA protection.
The information in this blog has been sourced using The Hackers News. You can read the full story here
Adversary-in-the-middle (AITM) attacks from Social Engineering
An AITM attack involves “deceiving users into believing they’re logging into a genuine network, application, or website.”
Through this hack, people can unwittingly give information to Cybercriminals.
An example of this is a spear-phishing email that arrives in an employee’s inbox.
MFA prompt bombing
This attack involves push notifications in modern authentication apps. After hackers access a password, attackers try to use the password to trigger the MFA prompt for the compromised account.
If the user inputs their details into the MFA prompt, the hackers will gain full access to the account.
Service desk attacks from Social Engineering
Hackers access helpdesks by “feigning password forgetfulness and gaining access through phone calls.”
If the proper verification checks aren’t in place, hackers may be granted access to an organisational environment.
Another way is to “exploit recovery settings and backup procedures by manipulating service desks to circumvent MFA.”
An example of this is when hackers contact a service desk claiming their phone is not functioning or is lost, then request a new account which is controlled by an attacker-controlled MFA authentication device. This will allow the hackers to gain control.
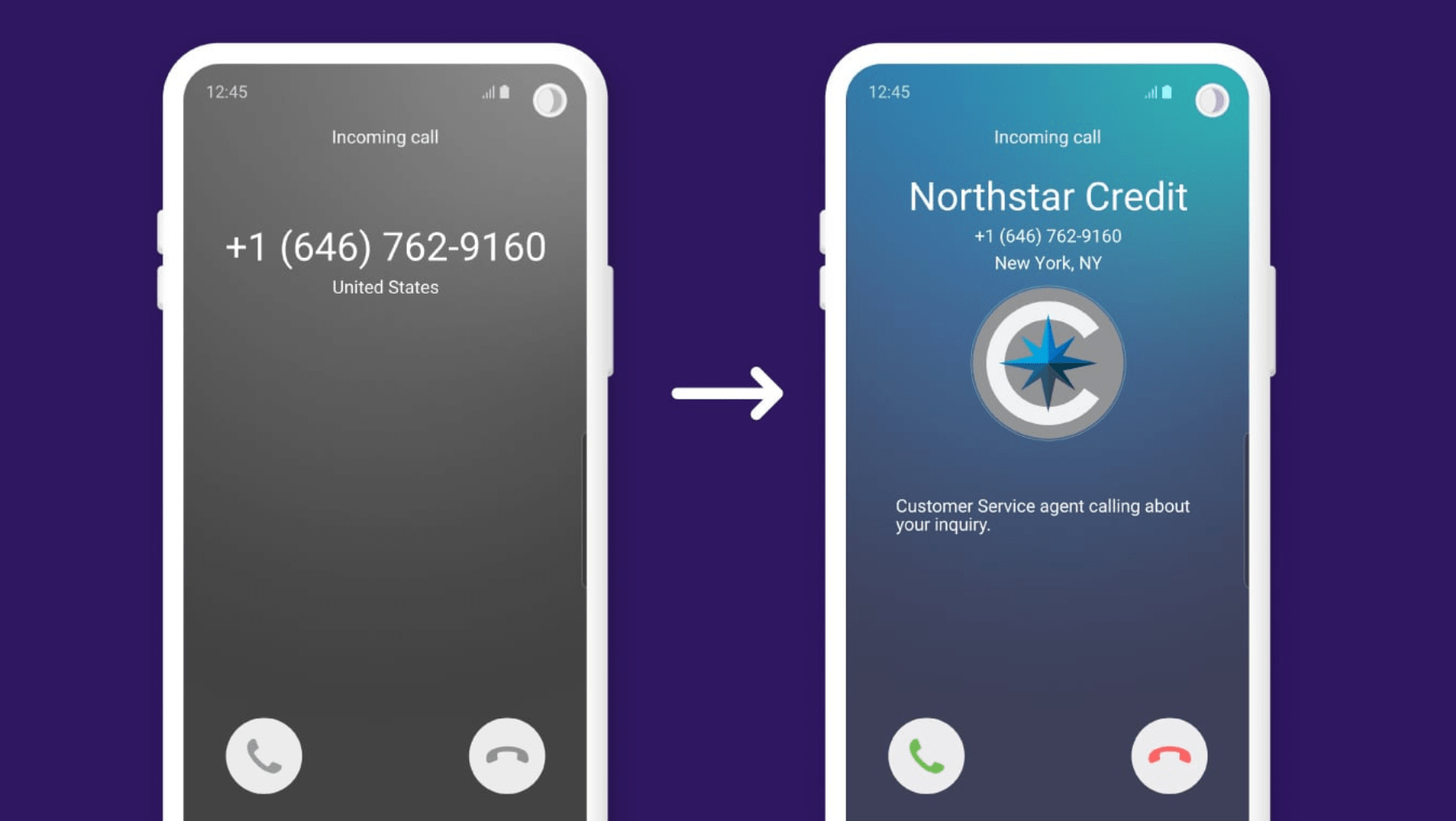
SIM swapping
This technique involves Cybercriminals deceiving “service providers into transferring a target’s services to a SIM card under their control.”
The hackers can then effectively take over the target’s mobile phone service and phone number, letting them intercept MFA prompts and gain full access to accounts.
If every member of your team spends 30 minutes a day on tasks that should take five (re-entering data, waiting for slow systems, copying
If your outbound calls are going unanswered, it may not be your team. It is your number. Across the UK, trust in phone calls
Most UK businesses are running three, four, sometimes five separate communication tools at once. Phone calls on one platform. Video meetings on another. Messages
According to the NCSC’s research, 87% of UK businesses do not meet the baseline standard for cyber resilience. That is not a statistic about
IT downtime rarely shows up as a single, obvious line on your P&L. There’s no neat figure labelled “lost productivity due to systems failure”
In recent years, many CEOs have found themselves operating in survival mode. Economic uncertainty, rapid technological change, talent challenges and shifting customer expectations have created a
Cybersecurity is no longer just an IT issue, in 2026, it’s a core business risk. For UK organisations of all sizes, cyber threats have become more frequent, more
Artificial Intelligence has rapidly moved from being a futuristic concept to becoming one of the most influential forces shaping modern business. Almost every sector is now
Winning more business is no longer just about a better pitch. It is about how easy you are to work with, how quickly you
Digital transformation has been one of the most overused business terms of the last decade. Yet for all the talk, many organisations still struggle