Since 2020, working from home (WFH) has become commonplace. In the wake of the COVID-19 pandemic, almost every company had to switch their traditionally in-office employees to some version of hybrid or remote work. Indeed, working from home became the new “normal” almost overnight.
The information for this blog was sourced from 11:11. You can read the full story here
WFH: Cybersecurity Challenges in a Hybrid Work Environment
Hybrid work does offer several challenges for cybersecurity that perhaps we never realised. For both the employee and the employer, cybersecurity has never been more critical — especially now that we’re connecting to our corporate networks from more locations and on more devices than ever before. For example, a cybercriminal now has even more ways (attack vectors) to prey upon employees or organisations. Data breaches, ransomware, and other cyberattacks have never been more sophisticated, pervasive, or ubiquitous, according to security experts at 4th Platform.
Here are some cybersecurity risks associated with the WFH/anywhere movement:
Expanded Attack Surfaces
With more employees working remotely, the attack surface in organisations has never been larger. More endpoint devices and networking connections greatly increase the workload for security staff.
Limited Oversight of Data Handling
Despite tools preventing the download of sensitive information to local devices, the reduced oversight outside the office heightens the chances of unintentional or malicious exposure of corporate data.
Compliance Challenges
Organisations might find regulatory compliance more challenging in work-from-anywhere environments. Remote workers can access and transport data in ways that violate the growing list of data privacy and protection laws.
Increased Susceptibility to Phishing and Social Engineering
Social engineering and phishing attacks are a threat to all workers, whether they are in the office or working remotely. However, such attacks tend to be more successful when aimed at remote workers. Research has found that people working from home can be more distracted and more likely to click on suspicious links. A new trend is attackers using AI to automate social engineering attacks. Remote workers, especially ones who don’t regularly meet in person with others, might have an even harder time distinguishing such attacks from legitimate communications.
Unsecured and Vulnerable Hardware and Networks
The combination of increased remote work and longstanding BYOD policies means many people use personal devices to do their jobs, regardless of whether they have the skills to adequately secure them.
WFH: Enhancing Cybersecurity with a Multi-Layered Approach
As these challenges indicate, hybrid and remote work pose demonstrable and unique cybersecurity risks. Individuals and organisations need to be vigilant when securing remote environments. Security essentials like Virtual Private Networks (VPNs), secure communication tools, and endpoint security are popular ways to improve security, but is that enough?
Of course, they are all important, but implementing a true multi-layered approach to cybersecurity is always best. If one area fails, there are additional layers to keep your data secure. Additionally, an effective multi-layered strategy should include zero trust security principles. Zero trust assumes that everything can be a threat, thus “never trust, always verify” is at its core. Implementing a zero trust strategy can significantly enhance the security of a remote or hybrid workforce by assuming that threats can exist both inside and outside the network.
WFH: Integrating Zero Trust into Cybersecurity
Here are four simple ways a zero trust strategy can be integrated into a multi-layered cybersecurity strategy for a hybrid or remote workforce:
Strong Access Controls and Authentication
Instead of a one-time authentication process, zero trust always validates user identity and access permissions while logged on to the network. Adding “Least Privilege Access” enforces the principle of least privilege, granting users the minimum level of access necessary to perform their tasks. This minimises potential damage from compromised accounts.
Enhanced Endpoint Security
Using enhanced endpoint security ensures that only trusted, compliant devices can access corporate resources. Devices must meet specific security standards and be continuously monitored for compliance.
Endpoint Detection and Response (EDR) and Managed Detection and Response (MDR)
Both EDR and MDR monitor endpoints for suspicious activities and respond to threats. MDR usually also includes managed “outsourced” monitoring to better detect and respond to security threats in real-time. This service would include advanced technology and skilled security analysts whose expertise is often in short supply and hard to retain if done “in-house.”
Secure Communication Channels
All communications should be encrypted end-to-end, ensuring data integrity and confidentiality even over unsecured networks.
Regular Security Training and Awareness Programmes
Training employees on an ongoing basis is critical to recognising and reporting suspicious activities and should never be discounted or ignored.
WFH: Embracing Zero Trust Architecture
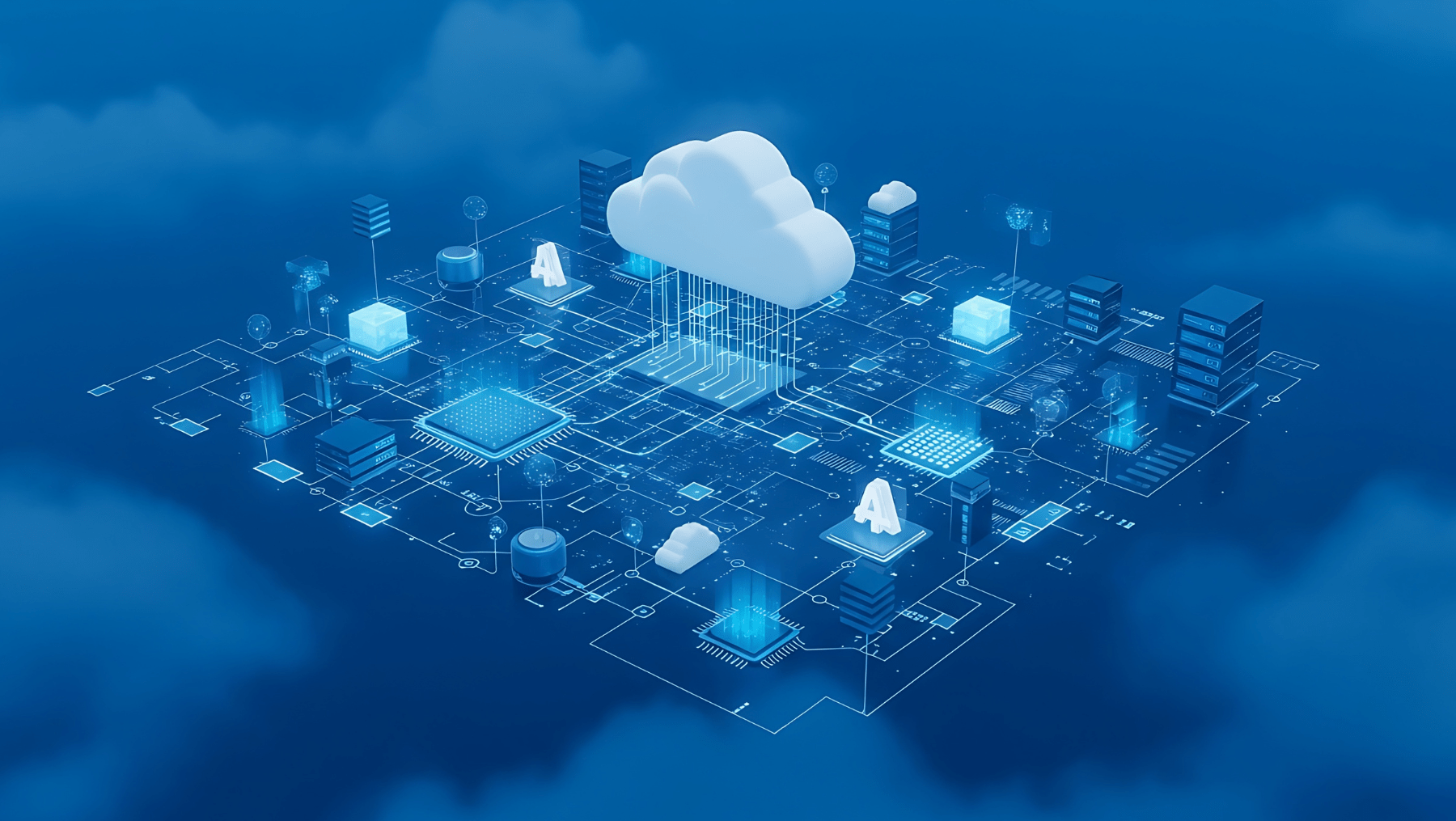
Employing zero trust architecture (ZTA) means focusing on securing data and ensuring that sensitive information is protected, regardless of where it is accessed or where it resides. Zero trust enforces security policies consistently across all devices and locations.
ZTA provides a comprehensive framework that supports identity and access management which ensures consistent application of zero trust principles across all users and devices. Security Information and Event Management (SIEM) solutions can aggregate and analyse security data, supporting continuous monitoring and threat detection.
So, while you might find working from anywhere to be a huge perk (and it is), it is also important that you understand the cybersecurity risks it poses to your company or organisation. I often miss the days of a four-digit login. I often complain about the effort that is required, especially when I am in a hurry, to log into my corporate network, or even to access my device. However, this is a small price to pay to safeguard both my personal and corporate data, which, for years, has been the lifeblood of any organisation.
Nobody wants to be the next security breach headline! Better awareness of cyber risks and security practices go a long way in securing both your data and your organisation’s data. When organisations integrate additional security measures along with zero trust principles, they can create a robust, adaptive security environment. Doing so better protects their remote and hybrid workforce from continual cyber threats — even when their dog decides to jump up on their lap in the middle of a video call!
Visit 4th Platform to learn more about how you can enhance your organisation’s cybersecurity.
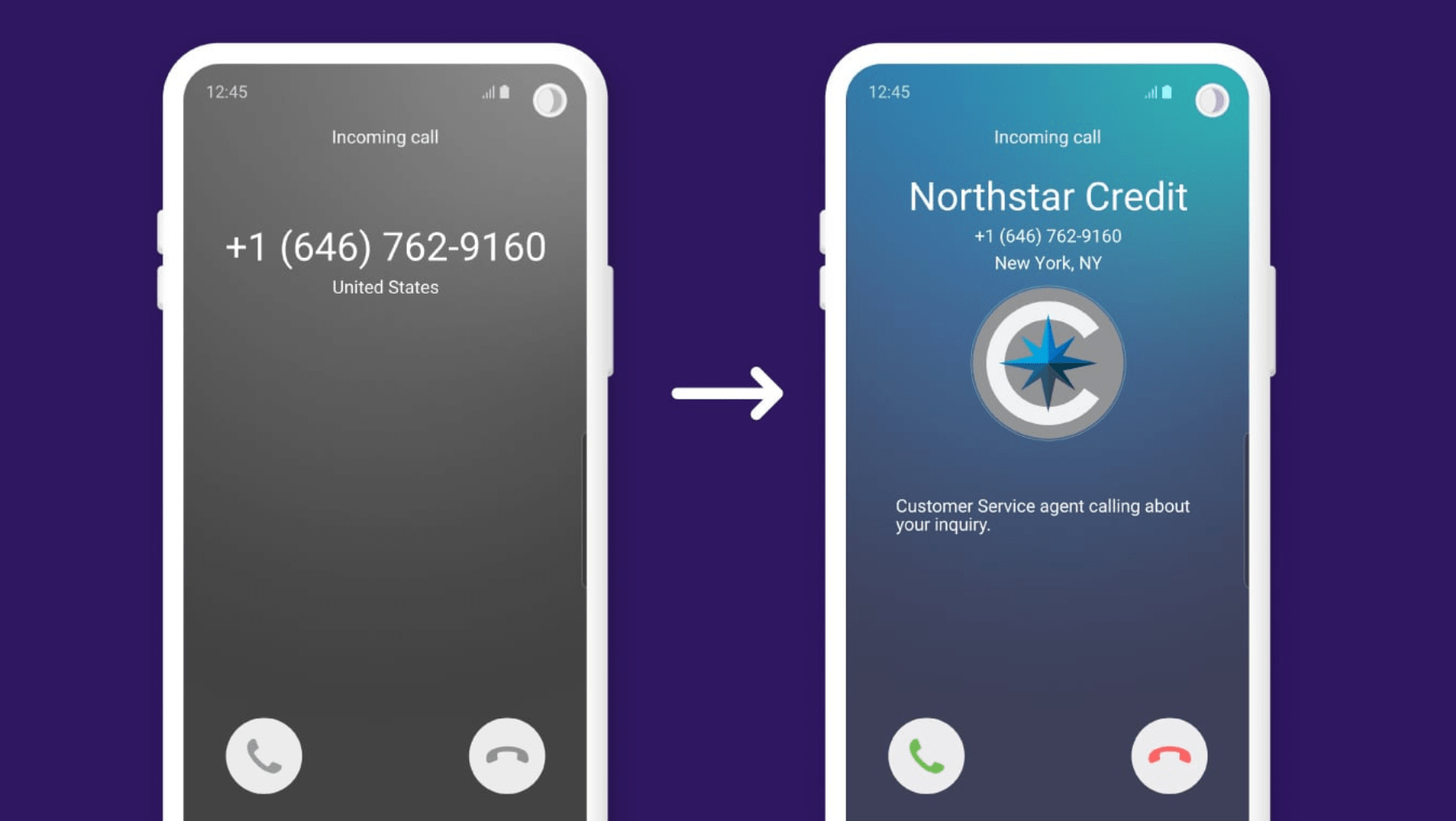
If your outbound calls are going unanswered, it may not be your team. It is your number. Across the UK, trust in phone calls
Most UK businesses are running three, four, sometimes five separate communication tools at once. Phone calls on one platform. Video meetings on another. Messages
According to the NCSC’s research, 87% of UK businesses do not meet the baseline standard for cyber resilience. That is not a statistic about
IT downtime rarely shows up as a single, obvious line on your P&L. There’s no neat figure labelled “lost productivity due to systems failure”
In recent years, many CEOs have found themselves operating in survival mode. Economic uncertainty, rapid technological change, talent challenges and shifting customer expectations have created a
Cybersecurity is no longer just an IT issue, in 2026, it’s a core business risk. For UK organisations of all sizes, cyber threats have become more frequent, more
Artificial Intelligence has rapidly moved from being a futuristic concept to becoming one of the most influential forces shaping modern business. Almost every sector is now
Winning more business is no longer just about a better pitch. It is about how easy you are to work with, how quickly you
Digital transformation has been one of the most overused business terms of the last decade. Yet for all the talk, many organisations still struggle
For many organisations, achieving Cyber Essentials marks a valuable milestone. It protects against the most common cyber threats, reassures clients and insurers, and establishes